OpenVPN using VPS
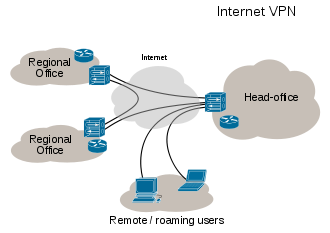 Virtual private network (VPN) extends a private network and the belonging resources across public networks like the Internet, allowing a host computer to send and receive data across shared or public networks as if it were a private network with all the functionality, security and management policies of the private network. This is done by establishing a virtual point-to-point connection using dedicated connections and/or encryption. OpenVPN, written by James Yonan, is an open source software application for implementation of VPN using a custom security protocol based SSL/TLS protocols, and is capable of traversing network address translators (NATs) and firewalls.
Virtual private network (VPN) extends a private network and the belonging resources across public networks like the Internet, allowing a host computer to send and receive data across shared or public networks as if it were a private network with all the functionality, security and management policies of the private network. This is done by establishing a virtual point-to-point connection using dedicated connections and/or encryption. OpenVPN, written by James Yonan, is an open source software application for implementation of VPN using a custom security protocol based SSL/TLS protocols, and is capable of traversing network address translators (NATs) and firewalls.
Implementation of OpenVPN using a virtual private server (VPS) is to extend the private network, from your local host as a client, to that remote server. In the following tutorial, I will show how to install OpenVPN on either a Yum Linux VPS or a Debian Linux VPS. I chose using Linux VPS because it is cheap; just $5 a year compared with $30/month of Windows VPS of the same configurations. If you prefer lightweight Linux distros then Debian is one of your choice.
- The first step is to check whether the /dev/tun device is enable on your VPS. This can be done using the follwing commands:
ls -al /dev/net/tun
cat /dev/net/tun
# If the device is enable then the results are as below,
# crw------- 1 root 500 10, 200 Dec 18 19:58 /dev/net/tun
# "File descriptor in bad state"
You may contact your VPS provider to have the device enable if needed. In the rest of this tutorial, I will show the installation commands for both the Yum platforms, in the first block, and Debian platforms, in the second block in every step.
- Make Linux' repos up-to-date then install OpenVPN
### Yum
yum -y update
yum -y install openvpn && yum -y install easy-rsa
### Debian
apt-get update && apt-get install openvpn
It is now good to go with the next steps for setting up point-to-point tunnel using OpenVPN which was installed as in the previous step. Assume that the remote server, which has the IP address x-xx-xxx-xxxx, is identified by "tinyray"; and your PC, the client, will be identified by "lnt".
- Create a folder for keys and certificates. Copy openvpn keys and configuration samples there.
### Yum
mkdir /etc/openvpn/sample && mkdir /etc/openvpn/easy-rsa
cp -rp /usr/share/easy-rsa/2.0/* /etc/openvpn/easy-rsa
cp -rp /usr/share/doc/openvpn-*/sample/sample-config-files/* /etc/openvpn/sample/
### Debian
mkdir /etc/openvpn/easy-rsa
cp -rp /usr/share/easy-rsa/* /etc/openvpn/easy-rsa
cp -rp /usr/share/doc/openvpn/examples/sample-config-files/ /etc/openvpn/sample
- Customize the key configuration: the server information, key and certificate encryption methods.
cd /etc/openvpn/easy-rsa/
# remove previously created certificates and keys
./clean-all
# enter the sub-shell
sh vars
# customize your openvpn
vi vars
# Make sure the following parameters are set; I choose encrypto key of size 2048
# export KEY_SIZE=2048
# export KEY_EMAIL="user@example.net"
# export KEY_CN="tinyray"
# export KEY_ALTNAMES="tinyray"
- Commit the server information and encryption settings
source ./vars
# If problem then
vi vi /etc/openvpn/easy-rsa/whichopensslcnf
# add the following into if block
elif $OPENSSL version | grep -E "1\.1\.[[:digit:]][[:alnum:]]?" > /dev/null; then
cnf="$1/openssl-1.0.0.cnf"
# then start over from "cd /etc/openvpn/easy-rsa/"
- Generate the Diffie-Hellman key for client-server communication
./build-dh
You should have the DH key generated or else, please redo from "./clean-all".
- Build the certificate authority
./build-ca
# press ENTER at every prompt to use the default value,
# but where it asks for "Common Name", please enter "tinyray"
# or whatever you choose for your server name.
- Generate server key and certificate
./build-key-server tinyray
# use the default values;
# leave "A challenge password" and "An optional company name" blank
- Generate client key and certificate
./build-key lnt
# use the default values;
# leave "A challenge password" and "An optional company name" blank
- Copy server key, certificate and dh key to openvpn folder
cd /etc/openvpn/easy-rsa/keys
cp tinyray.key tinyray.crt ca.crt dh2048.pem /etc/openvpn/
# please note that I choose encrypto key of size 2048
- Making OpenVPN server config file using the sample
cd /etc/openvpn/sample
### Debian— please additionally do the following job
gunzip server.conf.gz
vi server.conf
# please change: server.crt &rarror; tinyray.crt,
# server.key &rarror; tinyray.key, dh1024.pem &rarror; dh2048.pem;
# set max-clients to a reason number of users
# copy the server config file to openvpn folder
cp ./server.conf /etc/openvpn/
- Making OpenVPN client config file using the sample
cd /etc/openvpn/sample
vi client.conf
# change my-server-1 to x.xx.xxx.xxxx (the IP address of your VPS)
# change "client.crt" to "lnt.crt", "client.key" to "lnt.key"
- Export the four OpenVPN client files to /root which are then downloaded to client
cd /etc/openvpn/easy-rsa/keys/
cp lnt.key lnt.crt ca.crt /root
cd ../..
openvpn --genkey --secret ta.key
cp ta.key /root
cp sample/client.conf /root/client.ovpn
### Yum: Start OpenVPN service chkconfig --add openvpn && chkconfig openvpn on /etc/init.d/openvpn start # check if the service runs: ps -aux | grep openvpn
- At this point, you have successfully set up the tunnel between client and server. This tunnel however does not support internet connection through the server. To make this possible, you need to set up NAT (Network Address Translation) routing on the server (the remote host).
# /etc/openvpn/server.conf; update with the following
push "redirect-gateway"
push "dhcp-option DNS 8.8.8.8"
push "dhcp-option DNS 8.8.4.4"
#/etc/sysctl.conf
net.ipv4.ip_forward=1
# Issue the following command to support the above setting
echo 1 > /proc/sys/net/ipv4/ip_forward
# Issue the following commands to configure iptables # to properly forward traffic through the VPN
# Note: this step may be skipped by a system rebooting
# after having the following settings applied.
iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -A FORWARD -s 10.8.0.0/24 -j ACCEPT
iptables -A FORWARD -j REJECT
iptables -t nat -A POSTROUTING -o venet0 -j SNAT --to-source x.xx.xxx.xxxx
iptables -t nat -A POSTROUTING -o eth0 -s 10.8.0.0/24 -j MASQUERADE
# Copy these setting to "/etc/rc.local". Make sure this file exists on the system, otherwise need to make it following how to add "/etc/rc.local". Once ready: vi /etc/rc.local, looks like the following:
#!/bin/sh -e
#
# [...]
#
iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
iptables -A FORWARD -s 10.8.0.0/24 -j ACCEPT
iptables -A FORWARD -j REJECT
iptables -t nat -A POSTROUTING -o venet0 -j SNAT --to-source x.xx.xxx.xxxx
iptables -t nat -A POSTROUTING -o eth0 -s 10.8.0.0/24 -j MASQUERADE
exit 0
then: REBOOT
- The final step is to install OpenVPN client software on the client. The software is downloadable by clicking here.
- Running OpenVPN client the first time: Assume that the four exported OpenVPN client files were downloaded to the local folder 'd:/openvpn', run the OpenVPN client program,
- Select "Connection profiles",
- Select "Local file",
- Browse for "client.ovpn" in "d:/openvpn". The VPN connection will be then shown in the list of OpenVPN client programs, just click it and enjoy.
To make sure that you get OpenVPN work properly, just visit this website. If the input box shows the IP address of your VPS then you are done!.